PicoCTF 2025 – Red (Forensics Challenge Write-up)
Challenge Overview
CTFs are always full of surprises, and forensic challenges never fail to test our ability to uncover hidden information. This time, I took on the "Red" challenge in PicoCTF 2025, where I had to dig into an image to find the hidden flag. Here’s how I solved it.
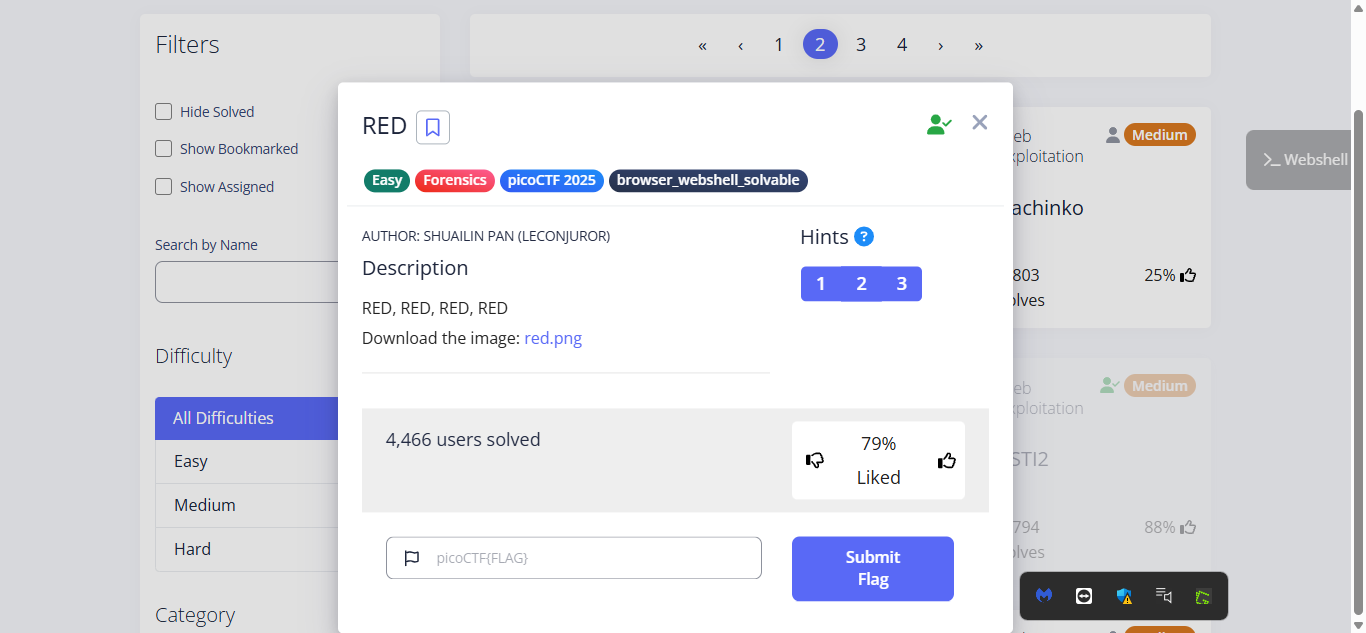
Downloading the Image
The challenge provided an image file named red.png. To download it, I used the wget command:
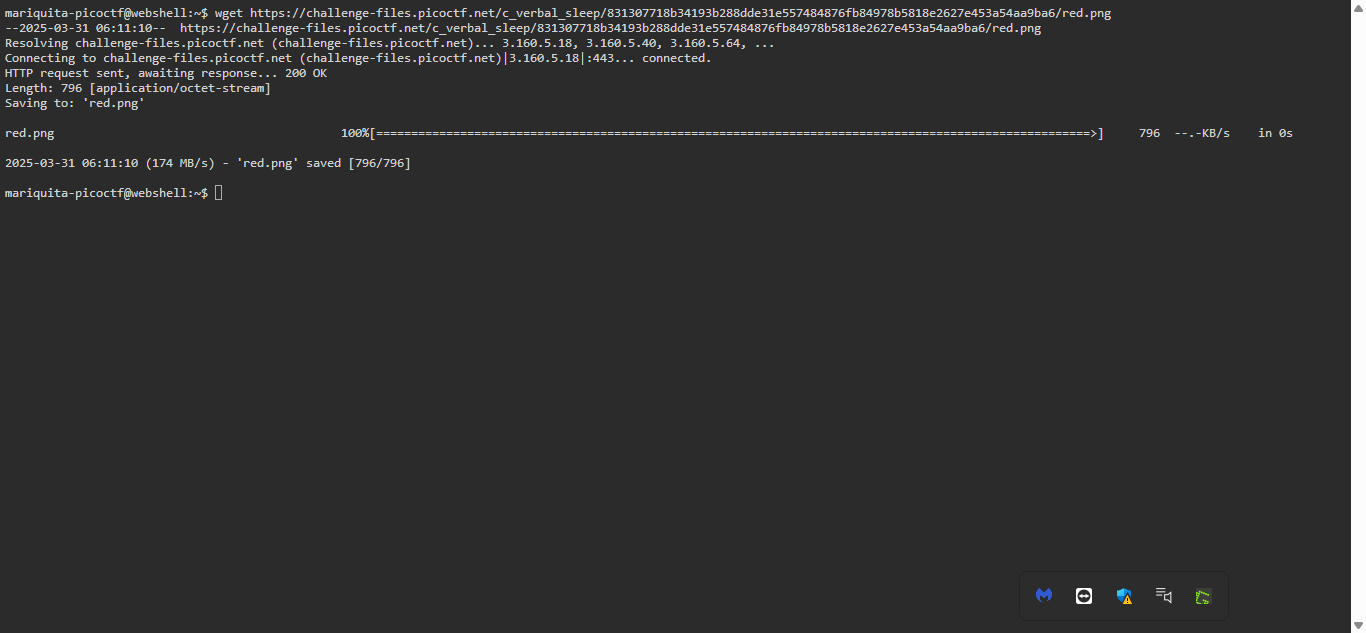
This saved the image directly to my system for analysis.
Extracting Metadata with exiftool
Metadata can sometimes hold important clues, such as hidden messages, timestamps, or software used to edit the image. A great tool for checking metadata is ExifTool.
What is ExifTool?
ExifTool is a powerful command-line utility used to read, write, and modify metadata embedded in images, PDFs, videos, and more. It helps in digital forensics by extracting information such as:
- Camera model and settings
- GPS coordinates
- Hidden comments
- Software used to edit the file
To inspect the metadata of red.png, I ran:
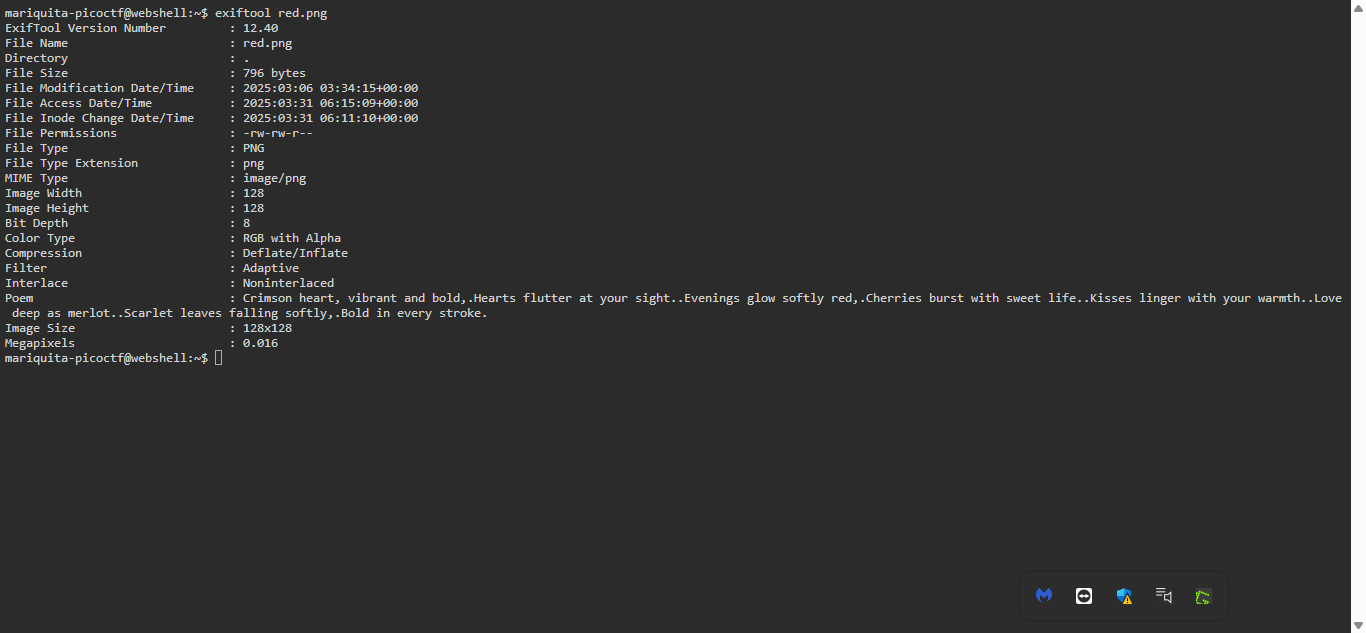
Unfortunately, nothing useful appeared in the output—no hidden text or suspicious metadata fields.
Using Steganography Tools
Since metadata didn't reveal anything, I suspected that the image might contain steganography—a technique used to hide data inside media files.
After researching, I found zsteg, a tool designed to analyze PNG files for hidden information. I decided to try it out
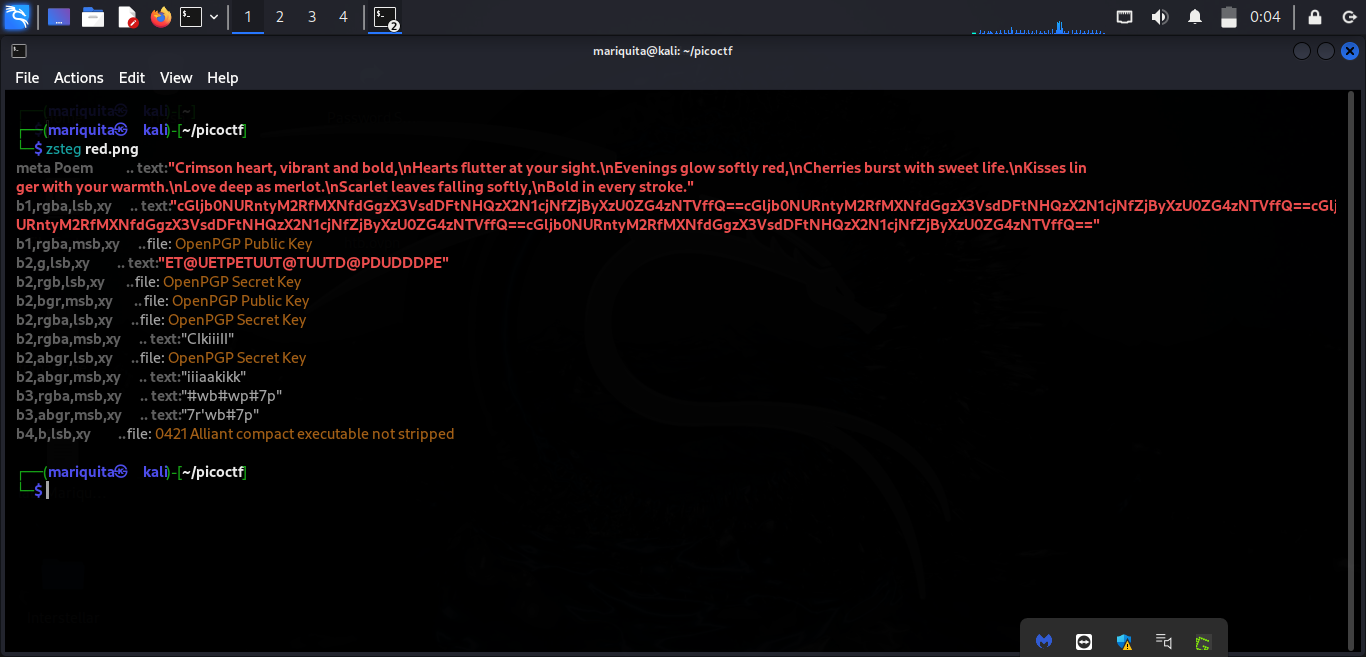
Boom! It detected hidden Base64-encoded data inside the image.
Decoding the Base64 Data
Base64 encoding is often used to conceal readable text. To reveal the hidden message, I copied the Base64 string and decoded it using:
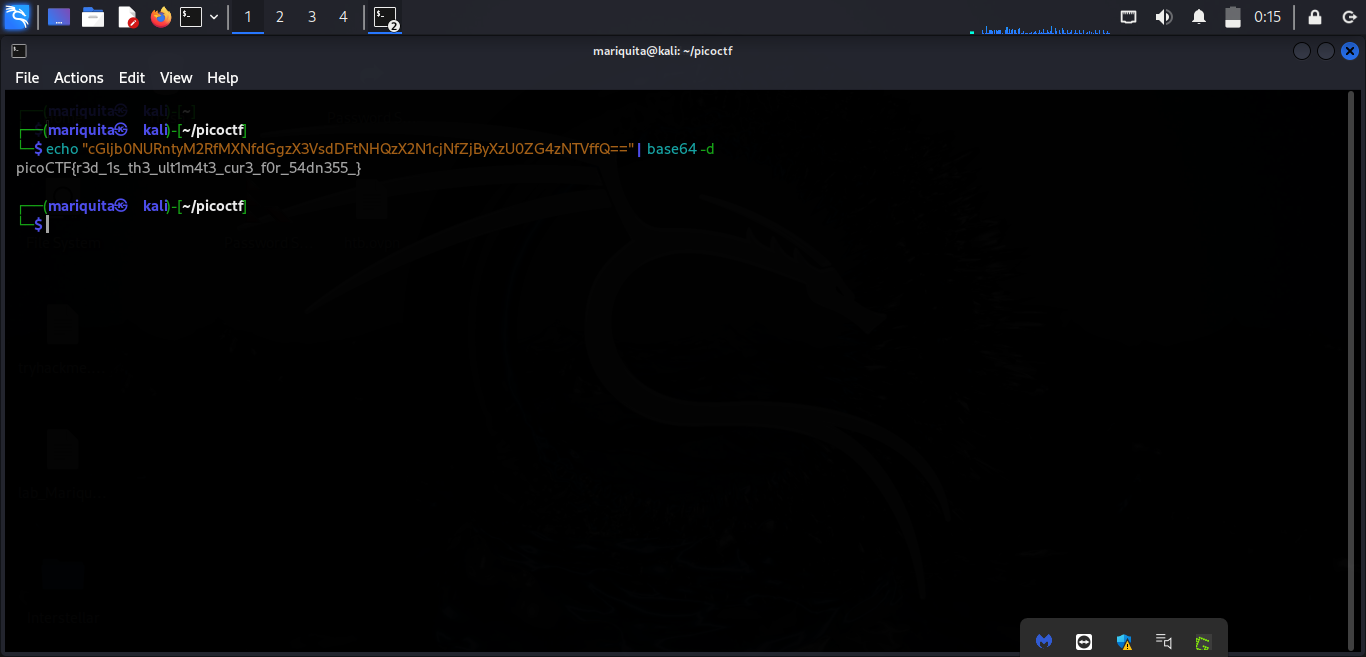
After decoding, I found the flag:
Flag:picoCTF{r3d_1s_th3_ult1m4t3_cur3_f0r_54dn355_}
Lessons Learned:
- ✅ Always check metadata first—it might reveal useful clues.
- ✅ If metadata doesn’t help, explore steganography techniques.
- ✅ Base64 encoding is commonly used to conceal text in images
This challenge reinforced the importance of metadata analysis and steganography detection in digital forensics. Although ExifTool didn't help this time, zsteg led me to the hidden message.
Until next time, happy hacking!